Identity Governance in Azure AD: Catalogs and Access Packages
IT security is important in any organization as we rely more and more on our IT infrastructure. Microsoft provides many ways to improve security, where identity governance within Azure AD is just one of them. This article will dive into the use of catalogs and access packages. After reading this, you will know what they are, how to use them and why your company wants them.
What is identity governance?
Identity governance is a policy-based an centralized way to manage identities and control access to company data. It is different to Identity and Access Management (IAM), because it enables your company to define, enforce, review and audit IAM policies and it can be used to define compliancy requirements.
Identity governance in Azure AD
A well-known example of an identity governance product within Azure Active Directory is Privileged Identity Management (PIM), which can be found in Azure Active Directory, under the Identity Governance blade. This is where you’ll also find entitlement management, which I found to be less known to many people.
What is entitlement management?
Entitlement management is one of the identity governance features that Azure AD has to offer. Entitlement can be described as a set of access rights to a set of resources, that a user can be granted access to. Within Azure AD, under entitlement management, you can manage these sets of access rights, known as entitlements. This is where you’ll find catalogs and access packages, on which we’ll zoom in some more.
Catalogs
Catalogs in Azure AD are a collection of resources: groups and teams, applications or sharepoint sites. A catalog can include as many of the above resources as desired, as well as combinations of the resources in each category.
For example:
Some members of the Marketing department of your work with an external company on a single project. The project members from the other company are guest users in your Azure AD tenant and need access to:
- a SharePoint site for this specific project;
- access to a specific virtual machine, which is made available to the Azure AD security group called Marketing Project;
- the Adobe Creative Cloud application.
You can include both the SharePoint site and the Marketing Project Azure AD group in one catalog.
It’s important to know that catalogs do not contain Azure resources themselves, such a storage accounts or virtual machines. However, the term resources is used in relation to Catalogs. These resources, in this specific context, can only consist of groups and teams, applications or sharepoint sites, as specified at the top of this paragraph.
Access packages
Now some members of the Marketing department from your own company need to work on the Marketing Project and will need access to a dedicated SharePoint site, only meant for the internal users. The internal Marketing users can request the access to the Marketing Project resources freely. You will also need to grant access to the Marketing Project resources for all external users, but you want to make sure that each request for access is approved by your Marketing manager. What is the safest and easiest way to do this? That’s where access packages come in.
Access packages pretty much give away what they are in their name. It’s a package that, if requested, grants access to a collection of resources.
Example
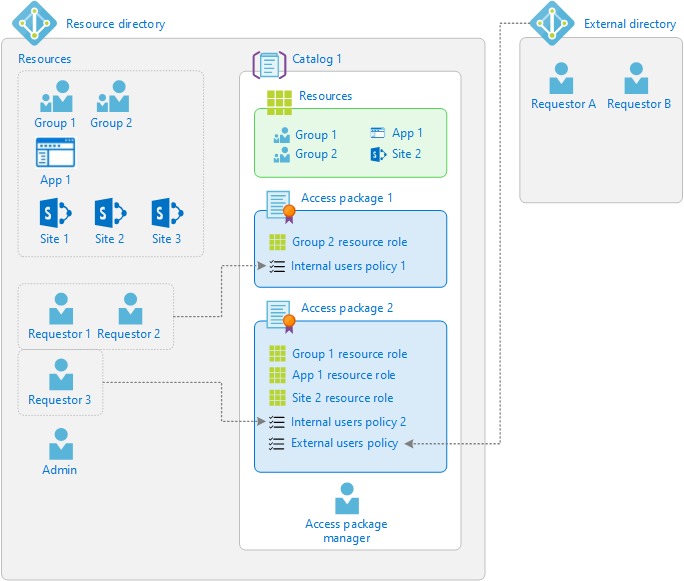
In this image from Microsoft, the use of catalogs and access packages is explained visually. This illustration will give you a global idea of the concept of catalogs and access packages and how they work.
How do catalogs and access packages work?
Let’s take the above example to clarify the use of access packages in combination with a catalog.
Within your Marketing catalog, you can add all the Marketing Project resources, including the SharePoint site that is meant for internal users only. You can now create two separate access packages:
- The first one will be for your internal users, which contains both the internal SharePoint site, as well as the project SharePoint site, the Marketing Project Azure AD group and this requires no approval from a manager.
- The second access package will contain only the project SharePoint site, the Marketing Project Azure AD group and before getting access, the Marketing manager will need to approve the request.
How to set up catalogs and access packages
We’ll look at how to set these up, step by step.
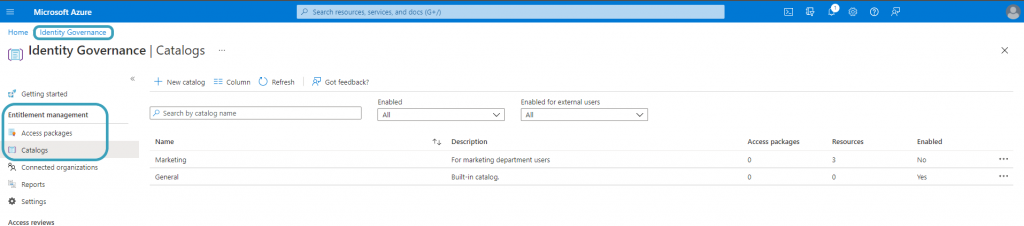
Catalogs and access packages can be found in Azure Active Directory, under the Identity Governance blade. You will find the Entitlement Management section, where you can choose catalogs and access packages. Access packages do not work without a catalog associated to it. You will have one built-in catalog, but no resources will be in there, unless you associate these resources with the general built-in catalog.
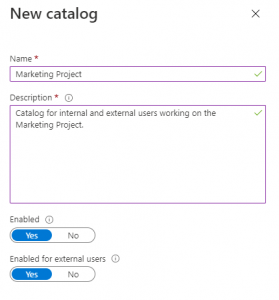
A catalog can be created by clicking the New Catalog button. You will be required to provide a name and a decription. You can enable the policy if you want to use it immediately, or set enabled to no if you want to stage the catalog. Make sure that if your access package will be available to external users, you will need to specify this.
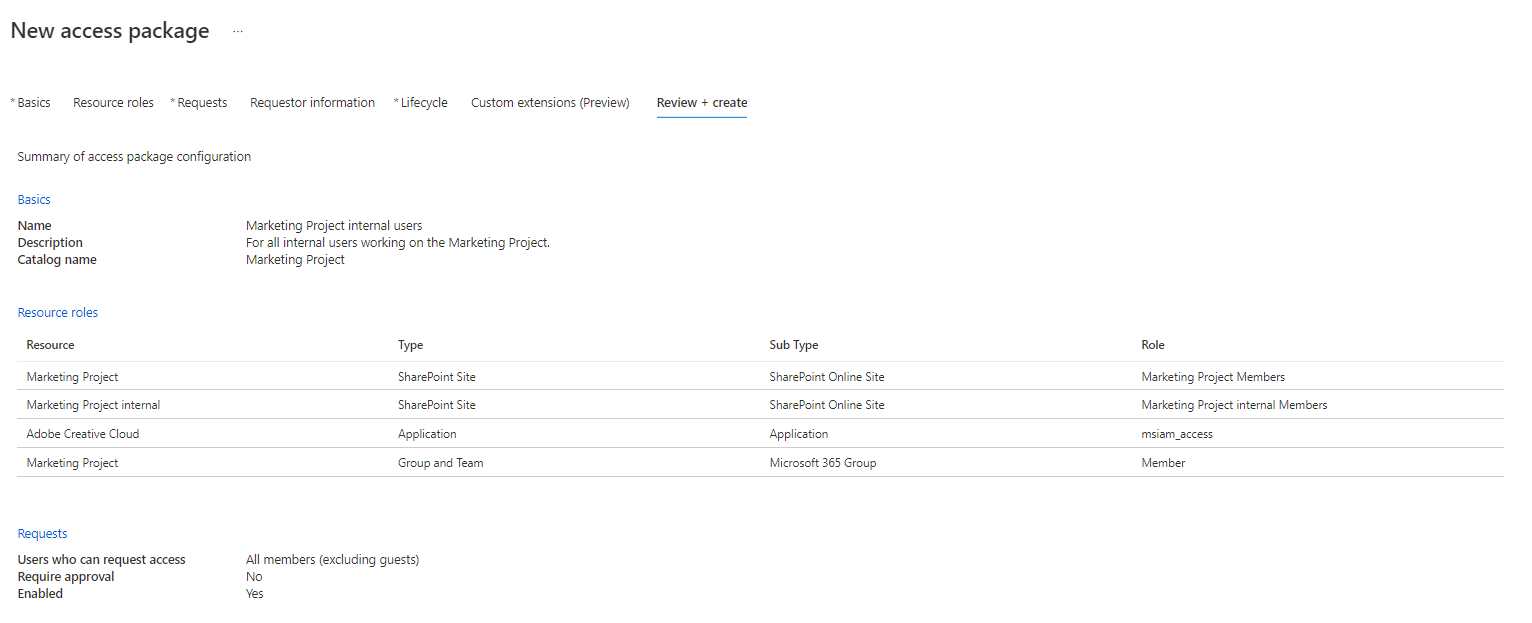
The next step is to click your newly created catalog, navigate to resources and click Add resources. You can add all resources needed in this catalog here, since you’re not yet specifying who will have access to what. In this case, I will add the Adobe Creative Cloud application, the Marketing Project group and team and the two SharePoint sites: Marketing Project and Marketing Project internal. Once you have added all your resources, you can move on to access packages. You will need to create two access packages, as explained before.
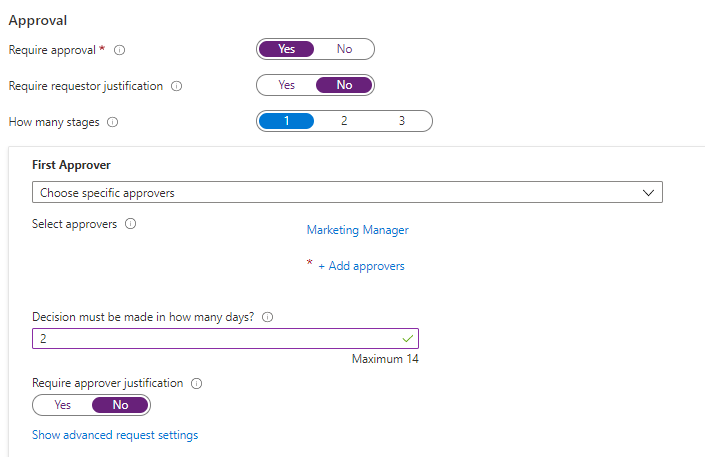
The second access package will look similar. However, it will not include the SharePoint site called Marketing Project internal. It will also require approval from a Marketing manager. You have several approval options, such as multiple people being able or required to approve the request, requiring justification for either the request or the approval and a deadline setting.
An interesting feature which makes this even more secure, is automatic expiration. The access package can be set to expire automatically on a specific date, after a specified number of hours or days or never. This will make sure that users will not have everlasting access to your resources. Let’s say the Marketing Project is scheduled to be finished on June 1st, we can expire the external users’ access on this specific date. Expiration policies can be added during the creation of an access package, or can be added later by editing the access package.
Why does your company want this?
Why would you use catalogs and access packages as part of your identity governance strategy?
As you can see, there are many options on keeping your environment safe and giving people the correct access to the correct resources for a limited amount of time. It will make governance so much easier, while making your users more self-reliant. There is no longer any need to call a manager or IT services to ask for specific resources, while that manager or IT services might not know exactly what you need for what project or whether you’re even allowed to request this access. The process of approval flows automatically from the access package, so your IT guy doesn’t have to go to the Marketing manager manually to request an approval. And with your expiration policy set, you will make sure that access will be removed once it is no longer needed.
Working on a project together with another company is one example where access packages provide the ideal solution. Other scenarios include time-limited access for employees, self-managed access to resources or access which requires approval. These scenarios can all be combined as well in one or more access packages and catalogs.
While security usually compromises a lot of convenience for your users, catalogs and access packages have the best of both worlds. They combine a secure way of working with a more convenient way of working. Are you planning on introducing catalogs and access packages in your company? Or are you already making the most out of them?